 Become a Partner
Already a partner ? Login
Become a Partner
Already a partner ? Login
Program
Partner Program Overview
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreInfrastructure
Quick Links
Case Study
Industry Solutions
Quick Links
Program
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreFeatured Topic
Newsletter
Gone are the days when an organization could trust everything within the four walls of its perimeter. Cloud computing, and accelerating digital transformation from an unprecedented pandemic have blurred the network perimeter. The COVID-19 crisis necessitated businesses to adopt remote working. This shift has increased the security risk posture of nearly every organization due to vulnerable access mechanisms, inadequate controls over unmanaged devices and infrastructure, putting additional pressure on security teams that are already resource crunched.
With the expansion of the attack surface, organizations have started to put “zero trust adoption” on their priority lists, regardless of whether they are fledgling start-ups or well-established enterprises. But this transition to zero trust is smooth only in theory. Zero trust implementation comes with its own set of barriers, and InfoSec leaders approach these challenges in different ways.
Given the challenges and the change in narrative from “who or what to trust” to “Never trust, always verify”, companies must look for ways to adopt a frictionless zero trust strategy so that the true benefits can be realized quickly and efficiently without disruption. They can best achieve this with a managed risk approach and by collaborating with trusted security partners who provide next-gen security solutions and the necessary expertise to help businesses manage their zero trust deployment without any hassles.
While zero trust has become a clear necessity in today’s enterprise networks, its implementation is often a topic of debate. While CISOs might be eager to adopt a zero trust framework across workloads, cloud, data centers, endpoints, and users, they can’t avoid organizational level challenges that decelerate zero trust adoption. Some of these barriers are:
“Visibility is the key in defending any valuable asset. You can’t protect the invisible.”
– Dr. Chase Cunningham, ForresterTM
The challenges listed above may seem daunting. But the benefits that an enterprise can derive from the successful implementation of a Zero Trust Architecture far outweigh the challenges. To get started with a zero trust implementation, here is a 5-step roadmap outlined by Forrester :
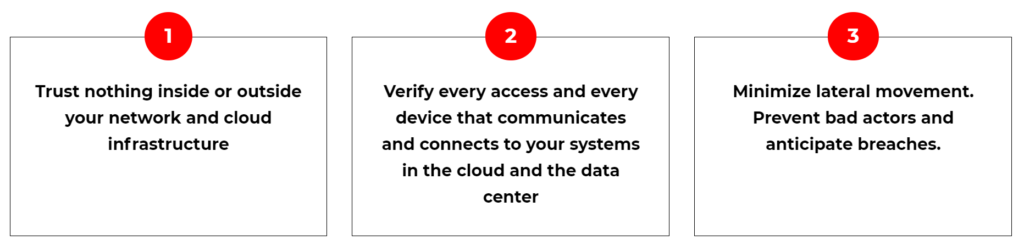
In simplistic terms, modern enterprises can implement zero trust in their network by following the critical steps below:
Post a successful implementation of a Zero Trust Framework , these are the benefits that an organization can achieve:
Operationalizing zero trust is a two-step process: the implementation of the solution, followed by the continuous threat assessment. In the modern complex threat landscape, organizations need to continuously stay one step ahead of threat actors, i.e. having a 24×7 Zero Trust Coverage of assets both inside and outside the network. Deploying a zero trust solution is the first critical step in combating threats.
But, since hackers manage to breach even the most secure fortress, a containment strategy is key to mitigating risk. A zero trust service that continuously monitors and defends with just-in-time response can help operationalize zero trust, especially if the organization doesn’t have the in-house manpower or expertise to implement it.
This calls for the need of an outcome-driven security-as-a-service that helps enterprises rapidly adopt the proactive zero trust security framework and augments it with a robust security that protects from advanced and hidden attacks, ransomware, and data theft attempts, that traditional defense mechanisms do not catch. So, enhance the security preparedness of your IT team with a frictionless zero trust implementation.
To learn more about how our clients maintain a consistent and elevated security posture by successfully implementing Zero Trust security, click here.
By submitting this form, you agree to ColorTokens
Terms of Service and
Privacy Policy