Zero trust is no longer just a concept or a set of principles. It has evolved into an architectural framework that can be implemented and scaled to secure complex enterprise networks. By understanding the architecture of a zero trust framework and deploying security solutions that are in line with zero trust principles, enterprises can implement zero trust security across data centers and hybrid, multi-cloud environments.
What Is Zero-Trust Architecture (ZTA)?
Zero trust architecture is based on the concept of “never trust, always verify.” In practice, this means that access to any resource within the network must be subject to specified trust dimensions, or parameters. Failure to meet these parameters results in denial or revocation of access. This is in complete contrast to previous security models that assumed implicit trust within the network perimeter.
Zero trust security in its true sense can be made possible only when enterprises adopt an architecture that supports the underlying concept of establishing trust across all internal and external communications.
“Zero trust (ZT) provides a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privilege per-request access decisions in information systems and services in the face of a network viewed as compromised. Zero trust architecture (ZTA) is an enterprise’s cybersecurity plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies.”
— National Institute of Standards and Technology (NIST), U.S. Department of Commerce
6 Key Tenets of NIST Zero Trust Architecture
Before diving into the architecture of zero trust, NIST recommends that a few basic tenets should be considered to ensure the success of any zero trust security implementation. These tenets form the foundation of an architecture that supports the principles of zero trust.
Defining Devices
For zero trust to be implemented fully, the enterprise needs to consider all data sources and computing services as resources. These may include devices that share data with aggregators, software as a service (SaaS), and different types of endpoints that connect and communicate with the network.Securing Communications
All access requests from assets must meet preset security requirements. The assets may be located on enterprise-owned network infrastructure or any external network — the same security verifications must be applicable to all. Trust can never be implicit.Session-Based Resource Access
Trust has to be established before authorizing access to any enterprise resource, and the trust must be applicable only for the duration of the transaction. Authorization of access to a specific resource cannot be extended to access a different resource.Attribute-Based Policy Enforcement
Policy is the set of access rules based on attributes that an organization assigns to a user, data asset, or application. These attributes could be device characteristics like software version, location, time of request, etc. Behavioral attributes defined by user and device analytics may also be considered based on sensitivity of the resource.Dynamic Authentication and AuthorizationGranting access, scanning and assessing threats, and continually reevaluating trust must be an ongoing process. Asset management systems and multifactor authentication (MFA) need to be in place along with continuous monitoring to ensure that reauthentication and reauthorization are based on defined polices.
Policy Fine-TuningEnterprises must collect as much information as possible about the current state of the network and communications, using this data to continually improve their security posture. Insights provided by this data help to create new policies where needed and fine-tune existing security policies to enforce proactive protection.
The Core Components of NIST Zero Trust Architecture?
According to NIST, implementing zero trust requires an architecture or framework with specific logical components. This architecture should monitor the flow of data into and within the network, as well as control access to resources to ensure that trust is never implicit.
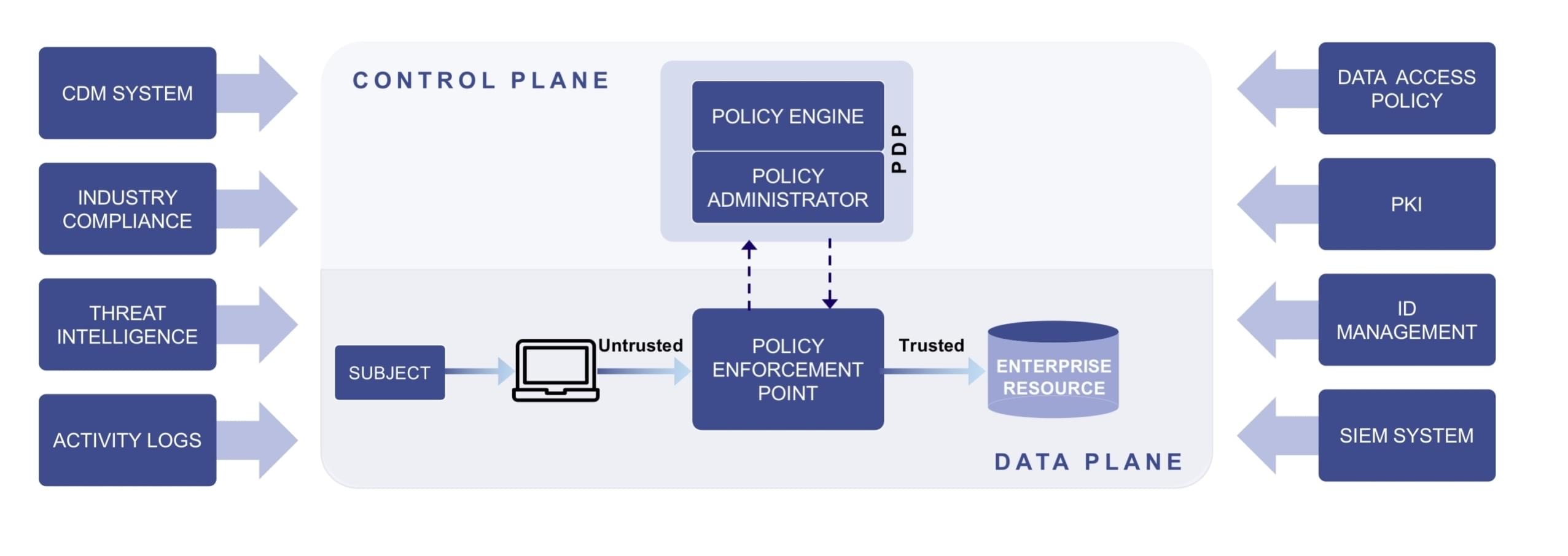
As such, verification is at the center of the zero trust architecture. Any and all access requests should be verified according to defined security policies before authorization. Considering how complex enterprise networks are, implementation of zero trust can be simplified by deploying solutions that allow context-based, dynamic policy enforcement across data center and hybrid cloud environments.
This can be achieved when the architecture has the following core components in place:
Policy Engine
The policy engine is the core of zero trust architecture. The policy engine decides whether to grant access to any resource within the network. It relies on policies orchestrated by the enterprise’s security team, as well as data from external sources like Security information and event management (SIEM) or Threat Intelligence to verify and determine context. Access is then granted, denied, or revoked based on the parameters defined by the enterprise. The policy engine communicates with a policy administrator component that executes the decision.
Policy Administrator
The policy administrator component is responsible for executing access decisions determined by the policy engine. It has the ability to allow or deny the communication path between a subject and a resource. Once the policy engine makes an access decision, the policy administrator kicks in to allow or deny a session by communicating a third logical component called the policy enforcement point.
Policy Enforcement Point
The policy enforcement point is responsible for enabling, monitoring, and terminating connections between a subject and an enterprise resource. In theory, this is treated as a single component of zero trust architecture. But in practice, the policy enforcement point has two sides: 1) the client side, which could be an agent on a laptop or a server; and 2) the resource side, which acts as a gateway to control access.
The Full View of Zero Trust
The zero trust architecture put forward by NIST is a detailed guide for enterprises and organizations to begin their zero trust journey. However, there is no one perfect method to implement zero trust architecture. To some extent, you could modify existing identity and access management tools to follow zero trust principles, but adopting the right security tools can make your zero trust journey simpler and efficient. A good start would be to look for solutions that provide real-time visibility of all network communications. Once you have a full view of your network, investing in a robust policy engine that can enforce policies across dynamic network environments can make implementation of zero trust possible — without increasing complexity.
Learn more: