 Become a Partner
Already a partner ? Login
Become a Partner
Already a partner ? Login
Program
Partner Program Overview
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreInfrastructure
Quick Links
Case Study
Industry Solutions
Quick Links
Program
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreFeatured Topic
Newsletter
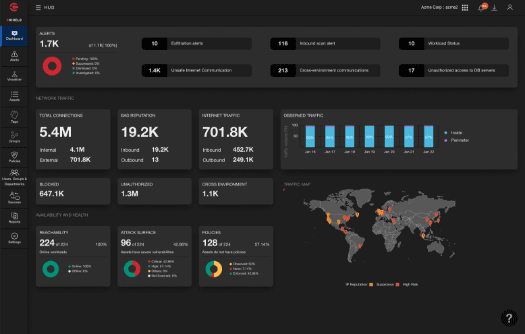
Xassure Managed Micro-Segmentation and Monitoring (MMS) delivers active deployment management and provides change management services for Xshield and Xprotect. Zero trust provides optimal security for the modern enterprise, which is increasingly cloud-based, perimeter-less, and supports a remote workforce. The service is aligned with NIST’s Zero Trust Architecture (NIST Special Publication 800-207). To support the future of care, electronic protected health information (ePHI), personally identifiable information (PII), electronic health and medical records (EHRs and EMRs), and the Internet-of-Medical-Things (IoMT) need to be safeguarded.
ColorTokens’ zero trust security approach provides unparalleled protection for healthcare and life sciences businesses.

"[The Xtended ZeroTrust™ Platform] is excellent when it comes to delivering Zero Trust …it fills the gap in any IT Environment."
IT Infrastructure Lead
Retail Organization
10B - 30B USD
Gartner® and Peer Insights™ are trademarks of Gartner, Inc. and/or its affiliates. All rights reserved. Gartner Peer Insights content consists of the opinions of individual end users based on their own experiences, and should not be construed as statements of fact, nor do they represent the views of Gartner or its affiliates. Gartner does not endorse any vendor, product or service depicted in this content nor makes any warranties, expressed or implied, with respect to this content, about its accuracy or completeness, including any warranties of merchantability or fitness for a particular purpose..
Take ColorTokens Xshield for a test drive.
See HowZero trust provides optimal security for the modern enterprise, which is increasingly cloud-based, perimeter-less, and supports a remote workforce. The service is aligned with NIST’s Zero Trust Architecture (NIST Special Publication 800-207).
The Zero Trust Adoption service (ZTA) uses a proprietary framework to deliver an outcome-driven solution and derive early business value from zero trust implementation. The ZTA framework addresses the following five dimensions of zero trust architecture:
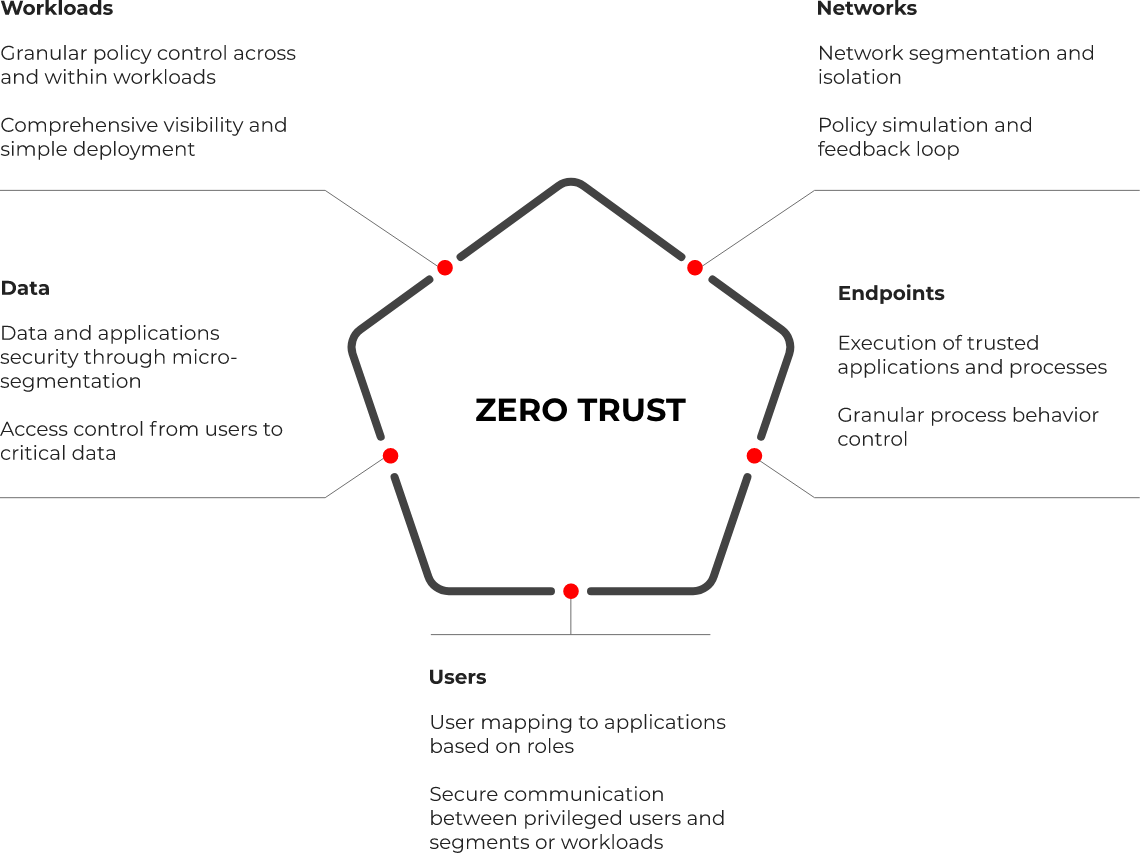
The service provides rapid deployment of Xshield and Xprotect agents on workloads, servers, and endpoints.
The service assesses the infrastructure architecture and configures the deployed products to ensure an optimized setup.
ColorTokens’ solution architects work very closely with IT teams to understand enterprise security requirements, priorities, concerns, network architecture, and existing policies. The solution architects then define micro-segmentation for workloads and servers. Security profiles are designed for endpoints, taking into consideration user profiles, authorized applications, and access.

Policies are designed to secure East-West and North-South traffic. Endpoint policies secure user compute devices from malware and any unauthorized process executions. Policies are simulated, observed for a period of time, and then enforced. This ensures minimal disruption to operations.
The service includes a subscription for the cloud-delivered products deployed.



Interested in procuring our services?
Platform
Learn MoreeBook
DownloadLearn More
By submitting this form, you agree to ColorTokens
Terms of Service and
Privacy Policy