 Become a Partner
Already a partner ? Login
Become a Partner
Already a partner ? Login
Program
Partner Program Overview
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreInfrastructure
Quick Links
Case Study
Industry Solutions
Quick Links
Program
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreFeatured Topic
Newsletter
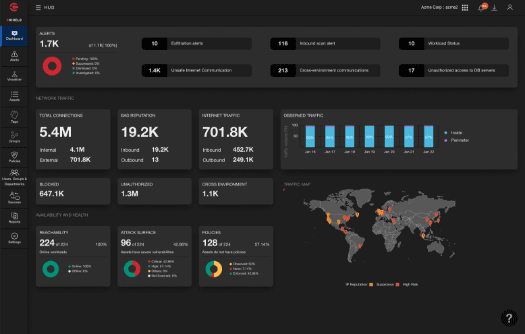
Breach Protection Service (BPS) leverages artificial intelligence (AI) and machine learning (ML), data scientists, threat hunters, and incident responders to detect sophisticated and hidden threats, advanced malware, and file-less attacks.
BPS uniquely monitors, correlates, and analyzes threats across networks, endpoints, and users to provide accurate detection of threats across enterprises and cloud-based assets, as well as early detection in the cyber kill-chain.
It provides deep and continuous analysis to hunt for traditional and targeted attacks designed to evade standard security technologies.

"I wish we knew about this [The Xtended ZeroTrust™ Platform] sooner."
Senior IT Manager
Retail Organization
500M - 1B USD
Gartner® and Peer Insights™ are trademarks of Gartner, Inc. and/or its affiliates. All rights reserved. Gartner Peer Insights content consists of the opinions of individual end users based on their own experiences, and should not be construed as statements of fact, nor do they represent the views of Gartner or its affiliates. Gartner does not endorse any vendor, product or service depicted in this content nor makes any warranties, expressed or implied, with respect to this content, about its accuracy or completeness, including any warranties of merchantability or fitness for a particular purpose..
Take ColorTokens Xshield for a test drive.
See HowBPS is designed to protect organizations against advanced and hidden cyberthreats that bypass traditional defenses. The service leverages threat models aligned to the MITRE ATT&CK™ framework to detect threats that can otherwise easily dodge traditional signature and pattern-based detection. The service provides an attack story that spans both network and endpoints to ensure a high rate of true positives in detecting anomalies or breaches.
BPS provides protection from advanced and file-less ransomware attacks out of the box. Machine learning-assisted behavioral analysis detects new variants of ransomware, user anomalies, and subtle data theft attempts. The service monitors for the slightest change in the way data is handled — copied, transferred, or transmitted — in or outside the network.
BPS includes incident response across endpoints and networks for faster containment and a kill-switch feature to stop the attack spread. Automated response rules detect and prevent the execution of advanced malware and untrusted software across endpoints and servers.
BPS includes a measurable security posture and quantified posture improvements. A well-defined success metrics program is rolled out with baselining at the beginning of the engagement. Xassure BPS delivers improvements on each success metric through regular defense checks and vulnerability identification to mitigate observed gaps.


Interested in procuring our services?
Platform
Learn MoreeBook
DownloadLearn More
By submitting this form, you agree to ColorTokens
Terms of Service and
Privacy Policy