Zero Trust Architecture (ZTA) is a security blueprint designed with the realities of today’s cyber threat landscape in mind. It’s based on the premise that attackers are already present, and at any point anything can be compromised – and in turn suggests organizations adhere to these key tenets of Zero Trust Architecture to maximize cyber resilience.
Broadly speaking, we can classify these ZTA tenets under three security domains. Using the NIST SP 800-207 document as a reference point, we’ll examine how these seven tenets of zero trust architecture fit into these domains, as well as why each tenet plays a vital role in ensuring robust Zero Trust security.
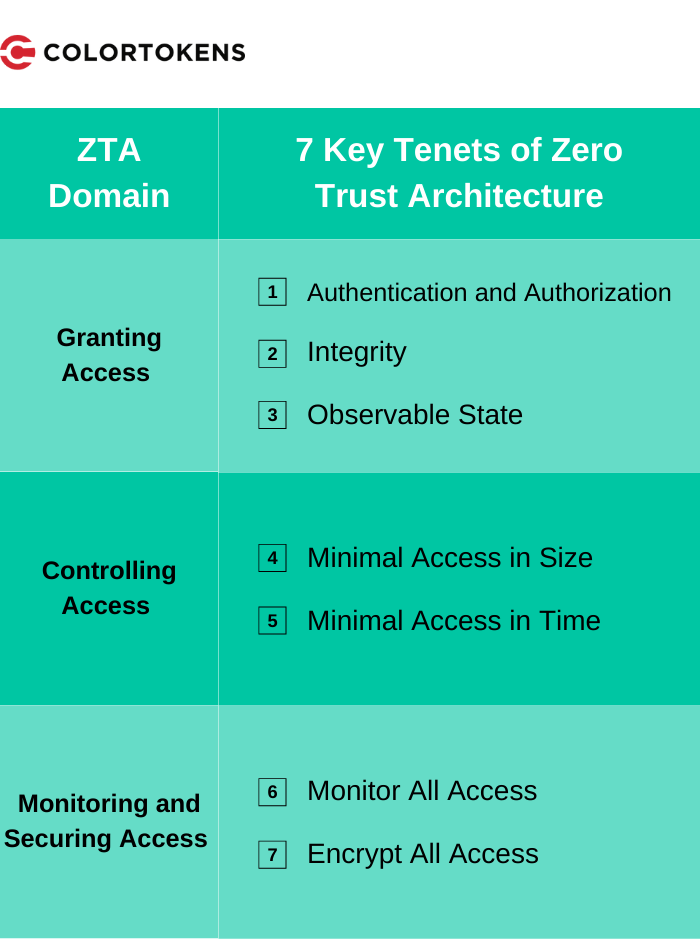
ZTA Domain 1: Granting Access
On what basis do we grant access? How do we determine and verify the identity of an accessor, the integrity of an accessor, and the state of an accessor? The three tenets in this category seek to address these critical questions; if these tenets are not properly implemented, unauthorized or compromised users or devices may get access when they should not.
Tenet 1: Authentication and Authorization
NIST – “All resource authentication and authorization are dynamic and strictly enforced before access is allowed.”
Broadly, this implies nothing is inherently trusted and everything trying to obtain access is properly authenticated with strong authentication (MFA, X.509, etc.), and even re-authenticated as needed.
Tenet 2: Integrity
NIST – “The enterprise monitors and measures the integrity and security posture of all owned and associated assets.”
Since we assume at any point anything can be compromised, integrity is continuously evaluated for vulnerabilities, patch level, and other possible corruptions which may compromise asset integrity.
Tenet 3: Observable State
NIST – “Access to resources is determined by dynamic policy—including the observable state of client identity, application/service, and the requesting asset—and may include other behavioral and environmental attributes.”
This tenet appears somewhat similar to the previous “Integrity” tenet, but the difference is that “Observable State” deals more with the characteristics and behavioral attributes an organization should evaluate before granting access. This may include location, device type, measured deviations, and unusual usage patterns.
ZTA Domain 2: Controlling Access
How much access do we grant, and for how long in terms of both time and activity? This aspect of Zero Trust Architecture relates the principle of least privilege. If it’s not properly implemented and we grant too much access, a small compromise can result in a massive breach.
Tenet 4: Minimal Access in Size
NIST – “All data sources and computing services are considered resources.”
Even extremely small footprint compute and data constructs such as containers, processes, functions, IOT actuators, files, DB tables, or data records are considered to be resources. It needs to be possible to control access to the minimal resource at the maximum granularity based on the need.
Tenet 5: Minimal Access in Time
NIST – “Access to individual enterprise resources is granted on a per-session basis.”
Access should be granted only to the individual resource, for the duration needed, and for the particular transaction. Access should be re-evaluated for every new transaction or after the shortest period of time necessary.
ZTA Domain 3: Monitoring and Securing Access
Once a Zero Trust access decision is established, access must be monitored and secured. If this aspect is not properly implemented – and we are not able to secure access for confidentiality or integrity, or respond to changes in the threat environment – we may not be able to protect our Zero Trust Architecture from network, infrastructure, and environment attacks.
Tenet 6: Monitor All Access
NIST – “The enterprise collects as much information as possible about the current state of assets, network infrastructure, and communications and uses it to improve its security posture.”
Enterprises should collect a lot of data about the overall security posture and threats in their environment. As these evolve, this context and insights should feed into policy creation and improvement.
Tenet 7: Encrypt All Access
NIST – “All communication is secured regardless of network location.”
The confidentiality and integrity of communications for the access request and the actual access are equally important to Zero Trust. If the communication and/or access request are compromised, manipulated, or breached, the whole Zero Trust premise stands invalid.
The Importance of Zero Trust Tenets
It’s vital that organizations properly address each of these tenets as part of their Zero Trust Architecture plan. If enterprises don’t have sufficient measures in place for even one tenet or domain, they may not be able to enjoy the benefits of a true Zero Trust Architecture.
About the Author: Satyam Tyagi is the Senior Director of Product Management at ColorTokens. He is an industry thought leader in security and networking, responsible for significant advances in endpoint, mobile, and application security. He has been awarded four patents in application security and networking, including products sold by Cisco and Avaya.













