Most of today’s organization’s data center deployment and operations are incredibly complex, as they not only have their own business-critical applications but also host their customers’ data. This presents a critical challenge in securing both their own and their customers IP.
To add to this complexity, these data centers will be a combination of on-premises, shared, or outsourced to a third-party data center for management and operations. Many customers host horizontal applications that are tenants of a larger data center that need to be separated from other workloads and customer environments.
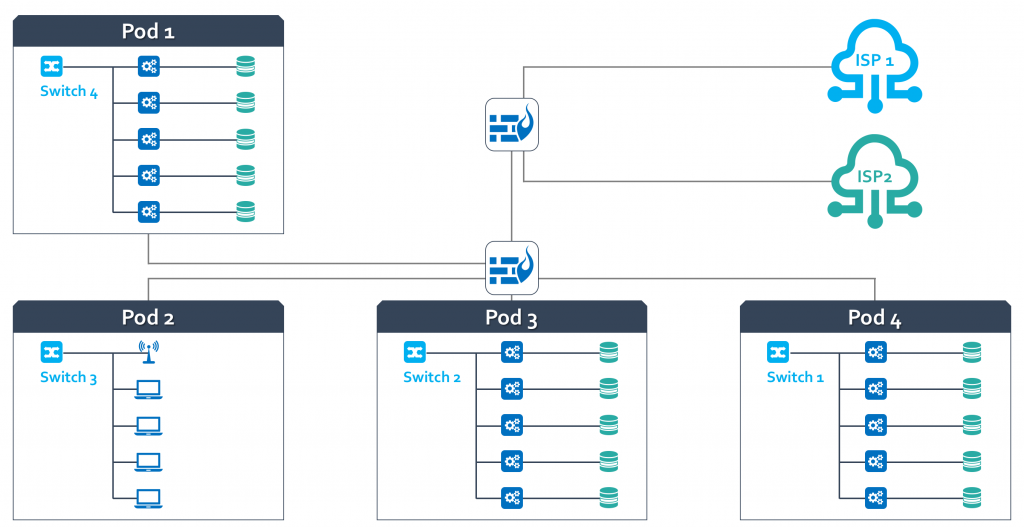
For example, PCI-compliant credit card or POS machines in a retail corporation are horizontal applications that are unique tenants sharing the same infrastructure. Although in this multi-tenant environment, these machines reside in the same infrastructure, it is critical that each pod/machine/environment is isolated from corporate business applications and other customer environments.
How Environment Separation Happens Today
Today, most customers will separate environments by creating a physical or virtual pod environment for their own and their customers’ needs. The environments are then typically segmented using VLANs, but as the environments and workloads scale you will run into one of the following scenarios:
- Sharing the pod and adding policies for network controls – leading to a greater number of ACL rules making it extremely hard to manage
- Build an entirely new rack or the virtual environment from scratch
In both scenarios, you face an incredible operational expense, and the ongoing management of the configuration will be painful.
Operational Challenges for Security Teams
- Lack of real-time visibility into workload traffic – can I see all the traffic between and across my environment and customers pods?
- Inadequate controls to separate environments to ensure there is no cross-environment traffic – how do I ensure traffic from POD 1 is not seen in POD 3?
- Inability to verify that policies are consistently enforced across workloads and move dynamically with the workload
- For real-time compliance monitoring – how can I prove that there is no cross-pollination between PODs or deviation from the corporate policies?
- Incredible operational expenses, as every time a new pod is being spun-up, the security team has to define a new set of policies, hindering the efficiency of implementing a new pod with appropriate policies.
- Inability to secure user access to a specific pod environment and make sure all other pod environments are undiscoverable to the user. How can I ensure that the user doesn’t have access to everything on the subnet?
Microsegmentation: An Effective Solution
To achieve microsegmentation in multi-tenant scenarios, your solution should be easy to implement and operate and provide you with the following:
- Real-time visibility into all environments and workloads and the traffic between them
- Enable you to create consistent and reusable policies that are independent of IP constructs and network infrastructure
- Quickly validate policies against real-time traffic, and then enforce
- Secure DevOps with workload security right away from the time of birth
- Continuous traffic monitoring and policy auto-correction
- Alert and auto-correct any deviation from the corporate policies
- Seamless and consistent policy enforcement across hybrid environments such as AWS, Azure, VMware, and GCP
See how ColorTokens’ award-winning security solutions can help improve your organization’s security posture. Register for a free demo today!