To understand Zero Trust Architecture (ZTA), one needs to first understand Zero Trust. There are several, somewhat evolving, definitions of Zero Trust in the security industry today, which can sometimes cause more confusion than clarity. Rather than introducing yet another definition, it’s worthwhile to take a step back and really understand the fundamental goal of Zero Trust instead.
Why Zero Trust
The goal of Zero Trust is to make organizations resilient to cyber threats by continuously identifying and eliminating uncertainty in enforcing security rules.
Let’s unpack that further.
“Resilient to cyber threats”
Enterprises are constantly under attack. For most, perimeter defenses have proven to be increasingly ineffective in stopping the initial breach or its spread. In such a context, “resiliency to cyber threats” refers to being able to maintain business continuity and data integrity even when attackers have breached defenses and may not yet have been discovered.
“By continuously identifying and eliminating uncertainty”
Enforcing security rules should neither be a guessing game nor involve making implicit trust assumptions. To the greatest extent possible, it should be deterministic. Also, enforcing security rules should be done on an ongoing basis, using several different input signals, even if it is for the same access request, as context and circumstances could have changed.
Key Elements of Zero Trust Architecture
Now that we understand the goal of Zero Trust, let’s switch back to Zero Trust Architecture. ZTA is exactly what its name implies. It is an “architecture,” or a blueprint, for implementing the principles of ZT. It is about going from a philosophy to a game plan.
As NIST (the U.S. Department of Commerce’s National Institute of Standards and Technology) describes it:
“Zero-Trust Architecture is an enterprise’s cybersecurity plan that utilizes zero-trust concepts and encompasses component relationships, workflow planning, and access policies.”
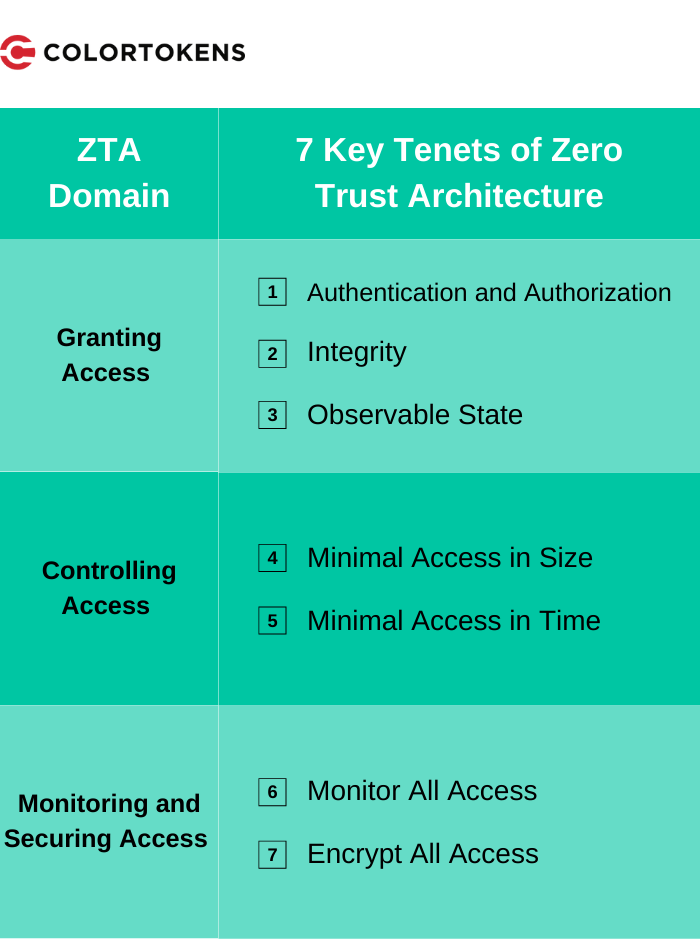
Extending this further, a Zero Trust Enterprise is one that implements this game plan. In order to implement this plan, the organization must find practical ways to lower or reduce uncertainties in enforcing security policies, and more specifically, access policies. Managing access to resources can be considered in three distinct domains:
- Granting access: What factors should be considered in allowing access?
- Controlling access: How much access should be granted?
- Continuous monitoring: How should organizations monitor changes in the security posture?
These domains cover seven key tenets of Zero Trust Architecture, which play a critical role in establishing strong security.
Zero Trust Architecture: Combating Modern Cyber Threats
In today’s digital world, perimeter-based security strategies often struggle to defend against increasingly complex cyber threats. ZTA is designed with the realities of the current threat landscape in mind: It rightfully assumes that enterprises won’t be able to detect and block every threat, and instead takes a “trust nothing, verify everything” approach to granting access, controlling access, and monitoring the security posture.
The ColorTokens Xtended ZeroTrust™ Platform is a cloud-delivered, software-defined platform that secures critical assets, including applications, endpoints, and workloads. The platform both simplifies and accelerates the enterprise journey to hybrid environments and full cloud adoption. Learn more about it here.
About the Author: Sunil Muralidhar is the Senior Director of Growth at ColorTokens. He is equally passionate about building business and developing world-class security products. Prior to joining ColorTokens, Sunil helped construct enterprise-grade system management and analytics solutions at Microsoft, VMware, and Tintri.