In part 1, we saw why it’s important to isolate your production, test and development environment. We also saw how environment separation is possible using traditional techniques, and the disadvantages.
In this concluding part, you will see how ColorTokens simplifies environment separation and improves the security posture of your data center.
Highly-secure environment separation in minutes
ColorTokens Xtended Zero Trust Platform enables secure microsegmentation to efficiently execute environment separation. ColorTokens is software-defined and platform-independent that seamlessly fits right into your multi-vendor, multi-cloud hybrid enterprise.
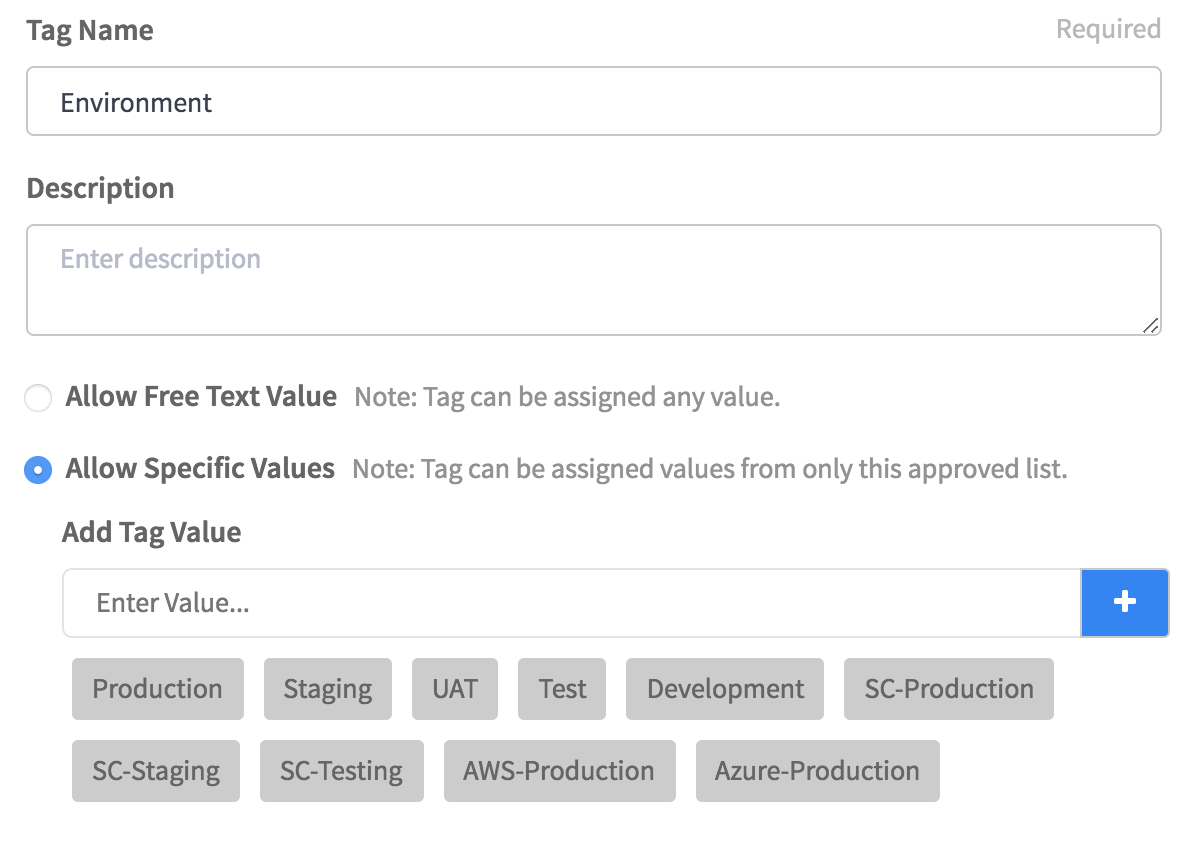
1. Simplified environment separation – Don’t deal with IP addresses and VLAN memberships. Based on abstractions, create reusable server roles, environment and application tags, that follow the resource wherever they move.
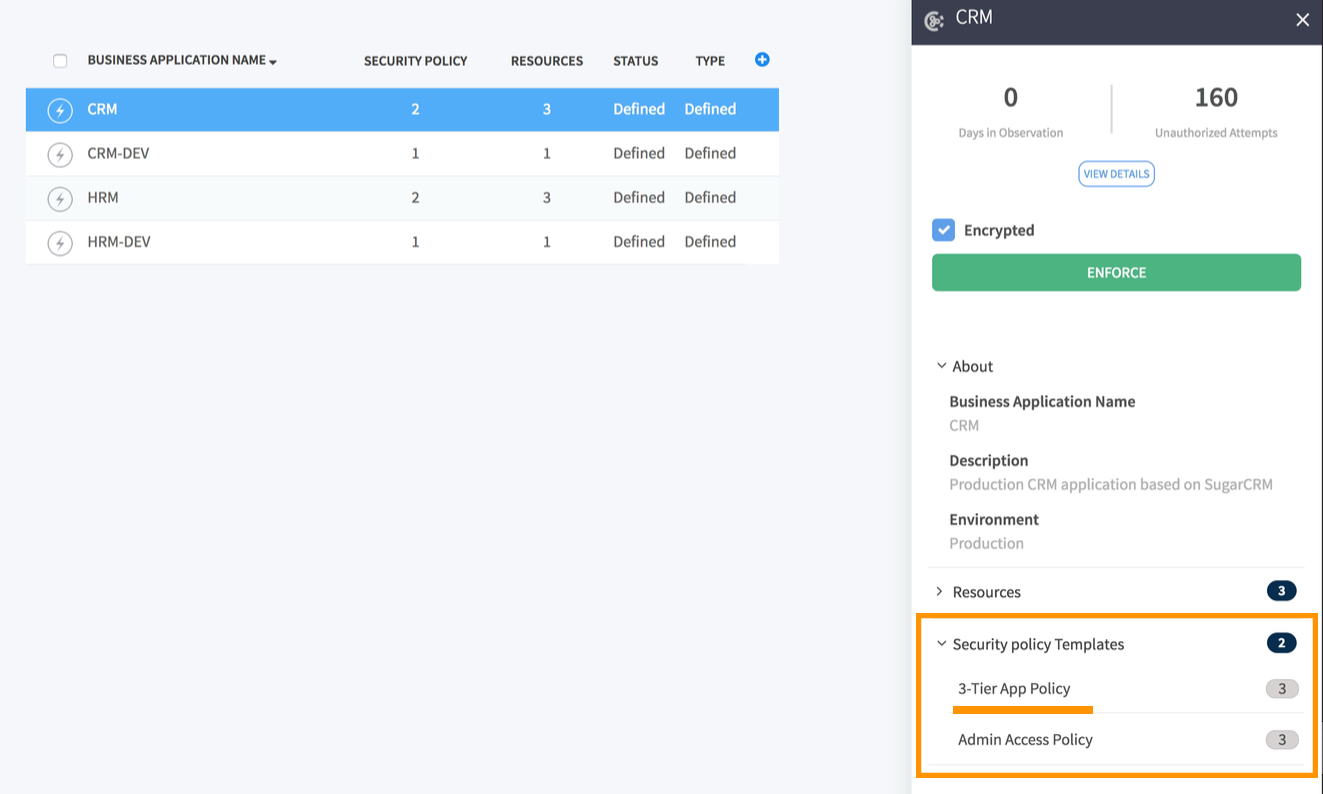
2. Automated security – Create reusable security policy templates that can be applied to the workloads and follows them wherever they move. Stop contamination of test and development environments with production data, ensuring data privacy and security.
3. Future-proof – Separate bare metal data centers and across multiple hybrid clouds. Manage your evolving data center environment from a single central console.
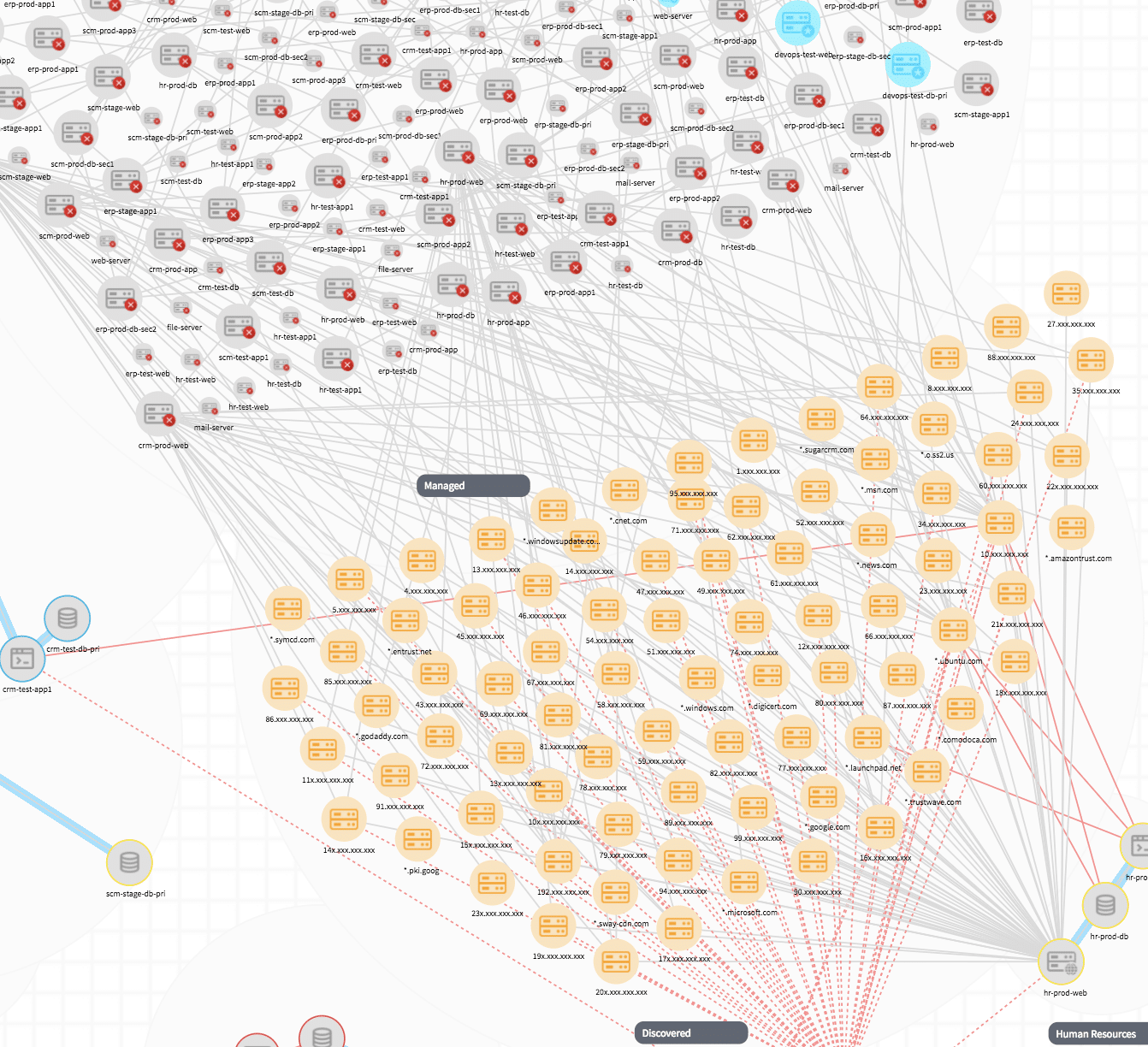
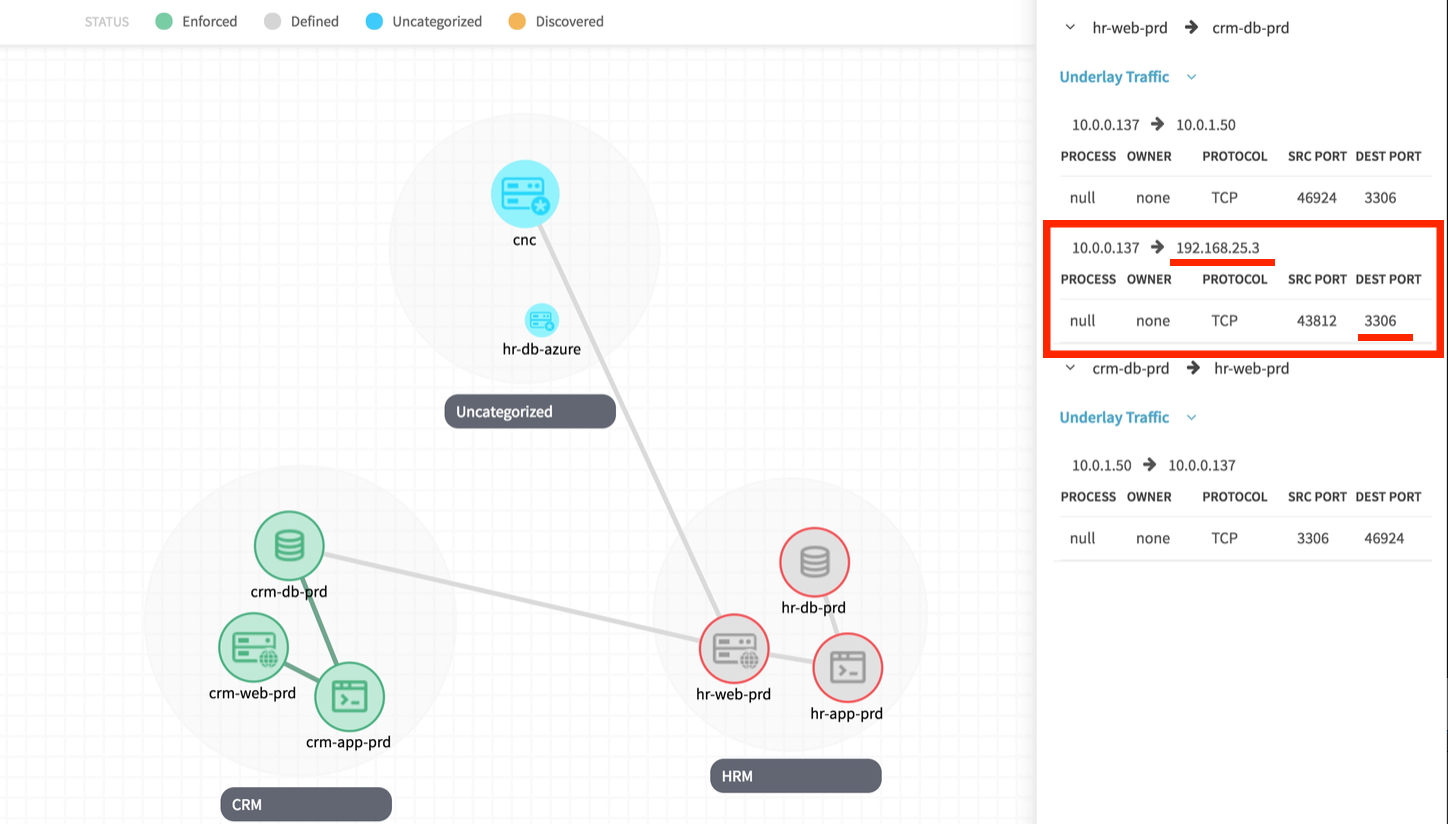
4. Comprehensive visibility and control – Create zero-trust networks with granular visibility into cross-segment traffic, across your multi-vendor enterprise environment.
ColorTokens Xtended ZeroTrust Platform provides a paradigm shift into how security can be enforced in large enterprises, without additional hardware and operational headache.
Learn more about environment separation using ColorTokens Xshield here.