Today’s data center is no longer a standalone /monolithic isolated environment but now spreads across multiple locations and data centers. In addition, workloads are dynamically being created and deleted/migrated across clouds. This phenomenon is exponentially increasing East-West traffic, making data center perimeters porous. Maintaining consistent policies across such hybrid environments is a challenge for most enterprises increasing their risk and exposure to data theft.
One of the golden rules of security is to use proper “segmentation” to protect your assets. This has become foundation for many of the compliance standards and security best practices.
With the increase in frequency and sophistication of cyber-attacks such as ransomware and data exfiltration enterprises are starting to adopt microsegmentation as a key defense, reducing their attack surface area. With microsegmentation you’re able to segment a network down to individual host, isolating the attack surface to single host.
Today’s Data Center Topology Stack
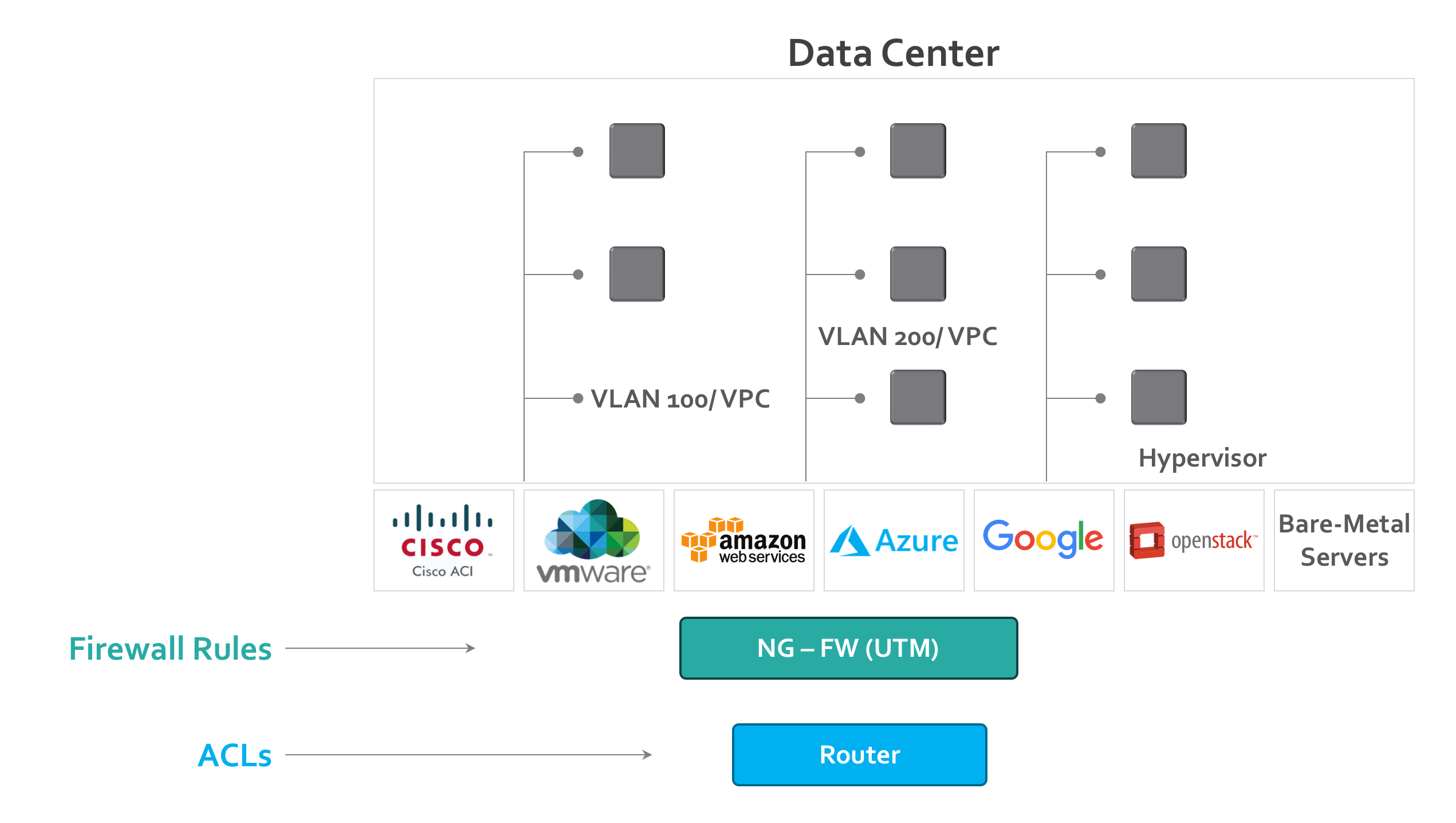
To protect the data center, we use several security products, from several vendors, at different layers of the OSI model.
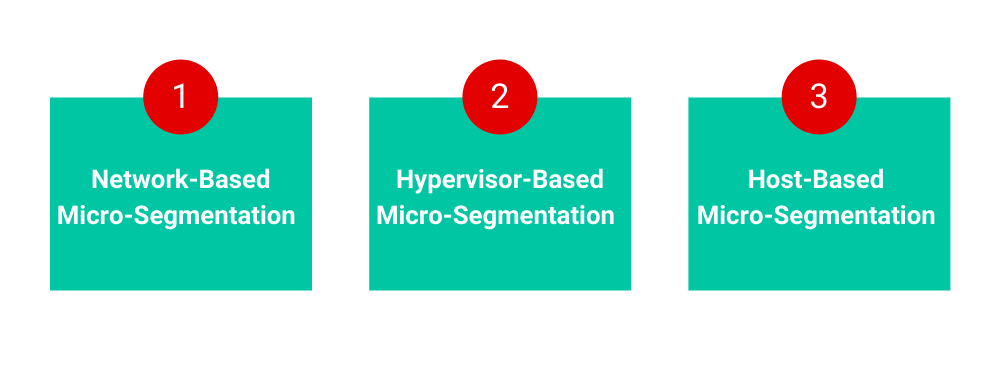
Approaches to Implement Micro–Segmentation
Depending on which layer of network you are most comfortable with, the following are the most commonly implemented microsegmentation techniques
- Network-based segmentation
- Hypervisor-based segmentation
- Host-based segmentation
1. Network-Based Microsegmentation
Network centric segmentation is primarily leveraging North/south access controls methods to E/W traffic. Policies are configured and enforced by implementing controls in network devices using ip constructs or ACLs . This process forces the admins to segment networks by vlan and the no.of resources in each vlan determines the attack surface, to reduce the attack surface to a single host one would have to create a vlan per host . For small networks one can leverage the perimeter firewall for E/W traffic management and for larger networks one will have to implement multiple instance across the datacenter.
Advantages:
- Most of the Network teams are familiar with implementation as it been around for a while
- Firewall rules are managed and enforced outside the workloads or hypervisor
- Leveraging perimeter firewall for both N/S and E/W traffic
Disadvantages:
- Network centric approach, one can end up creating macro-segmentation instead of microsegmentation, increasing the attack surface
- Difficult to have fine grained/micro policies at work load level and agility of moving same policies across environments
- Large no. of ACL’s or security policies in a dynamic datacenter are extremely complex to manage and keep updated across environments
- Security fault domain is defined by no. of resources in the segment
- Can become very expensive with security inspection
- In a public cloud implementation in addition to cost of firewall there is also cost of running multiple VM’s to support firewall function (minimum 2 for HA)
- Performance impact based on gateway bottlenecks
2. Hypervisor-Based Microsegmentation
The landscape of the modern data center is rapidly moving towards software defined datacenters with virtual workloads. As all the workload traffic has to go through the hypervisor, network isolation and microsegmentation can be done in the hypervisor itself and this approach leverages the functionality of the hypervisor firewall to provide visibility and micro-segment the workloads.
Advantages:
- Programmable overlay networks and policies
- Policy is enforced outside the workload on the hypervisor itself
- Agility to move policies along with overlay network and workload
Disadvantages:
- Support for bare metal /physical workloads
- Hypervisor and vendor specific
- Limited or no support to public cloud environment
- No support for container workloads
- Lack of process visibility
- Performance impact (CPU impact natively on the hypervisor)
- Number of policies supported by hypervisor
3. Host-Based Microsegmentation
As all the modern data centers or cloud environments are designed to address the on-demand/auto scaling, distribution, and migration of workloads across locations, host-based segmentation leverages the native firewall functionality built in the workloads itself to provide distributed and fine grained policy controls.
Advantages:
- Completely independent of any type or version infrastructure and hypervisor
- Works across any host OS environments
- Works seamlessly across distributed environments across data centers, cloud, bare metal
- Independent of any network changes (deploy one VM or thousands in minutes)
- Policy Agility along with the workloads
- Granular context awareness and visibility from each workload
- Insights into process running on each workload to address issues like dynamic port range etc.
- Stop unauthorized traffic even before it is on the network
Disadvantages:
- Need to install an Agent on each host
- Proprietary OS and legacy system support