 Become a Partner
Already a partner ? Login
Become a Partner
Already a partner ? Login
Program
Partner Program Overview
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreInfrastructure
Quick Links
Case Study
Industry Solutions
Quick Links
Program
Designed to deliver unparalleled customer value and accelerated mutual growth by harnessing partner expertise and ColorTokens cybersecurity technology.
Learn MoreFeatured Topic
Newsletter
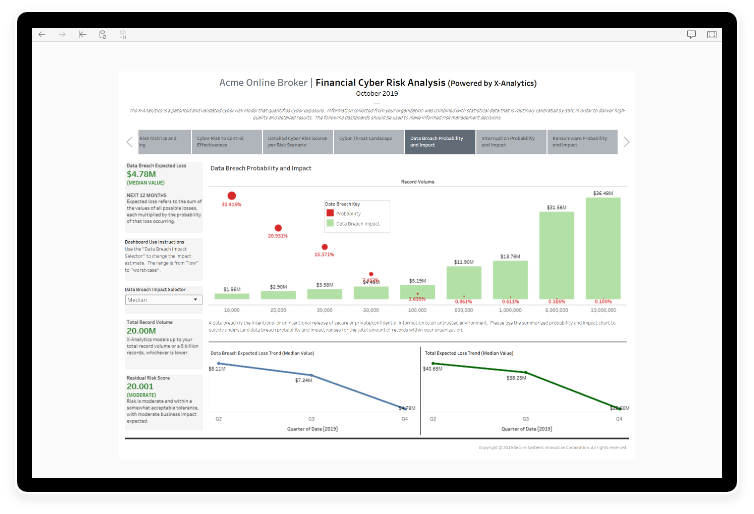
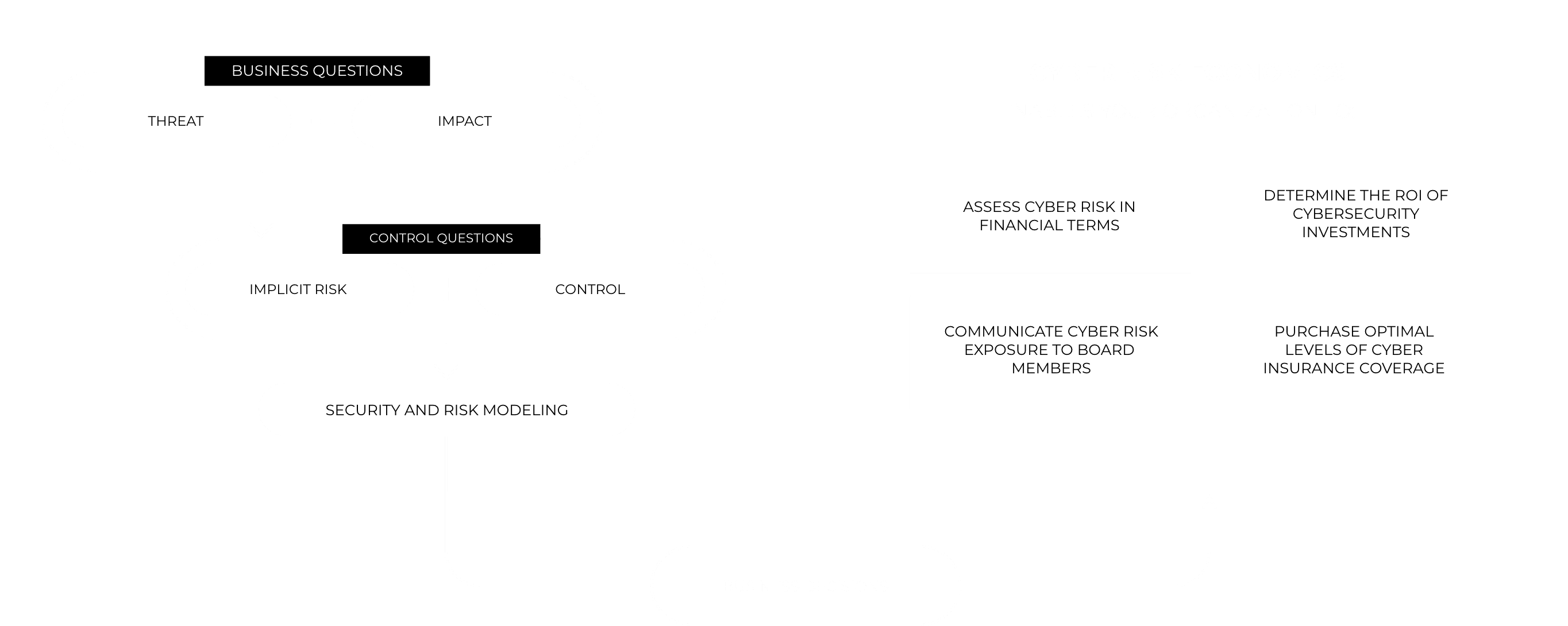
We use an industry-leading tool to quantify cyber risk in financial terms ($, £, €).
We base predictions on real data about historic cybersecurity incidents, which are updated on a monthly basis. Predictions are also based on a model that is regularly reviewed for accuracy by actuaries working in the cyber insurance industry.
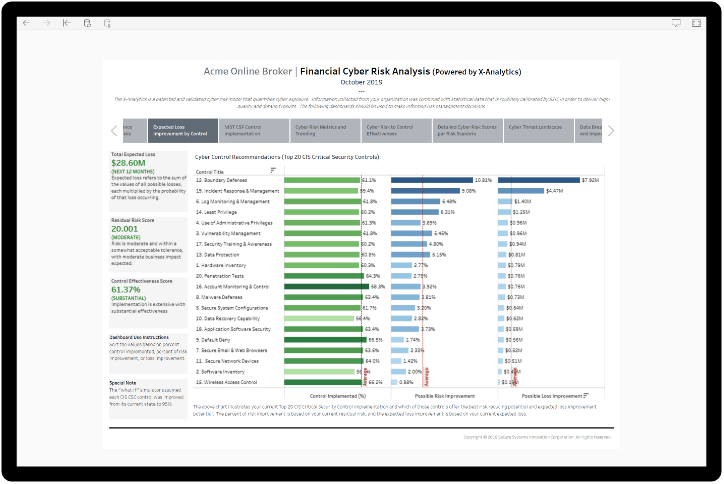
We assess your security controls against either the Center for Internet Security Top 20 Critical Security Controls or the NIST Cybersecurity Framework.
Economic quantification of your cyber risk enables you to make business decisions about control improvements by comparing the cost of the control against the potential risk reduction.
As a CISO, you’ll be able to request funding for projects that demonstrate financial business benefits.
Understanding your financial exposure enables a more cost-effective risk transfer to cyber insurance.
We offer regular reviews at a frequency that suits you to assess the financial risk reduction impact of security control improvement projects.
We review the implicit risk profile of your business to take account of changes in your business and in the external threat environment.
Our portal provides tracking data that enables reporting on risk reduction and a range of other metrics.
Data Loss: the cost of losing regulated data
Business Interruption: the cost of not being able to do business for a period of time
Ransomware: the cost of ransomware attacks of different durations
Misappropriation: the loss of intellectual property, business plans, and more
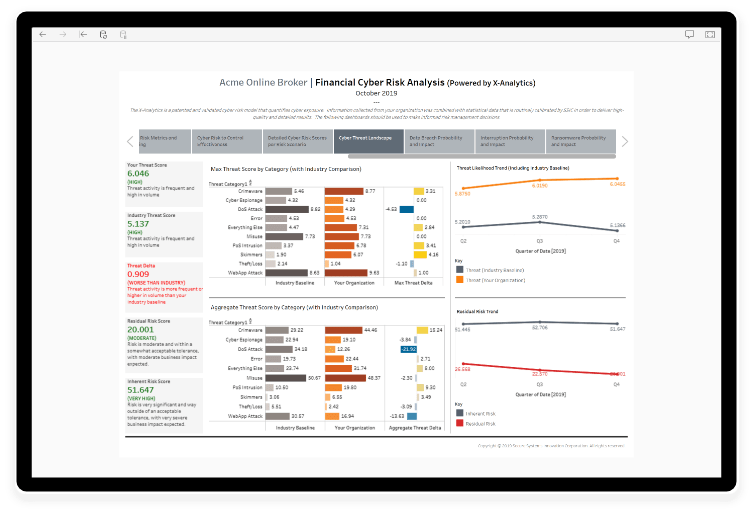
Identify the key threats facing your organization
Compare the threats that your organization faces to the industry baseline data
Review the changing threat landscape as implicit risk data is updated monthly
Improve incident response times by leveraging security intelligence and attack path analysis
Receive Assessments of the cybersecurity control effectiveness against the attack vectors
Get a ranking of the residual risk factors for each attack vector to enable prioritization iness plans, and more.
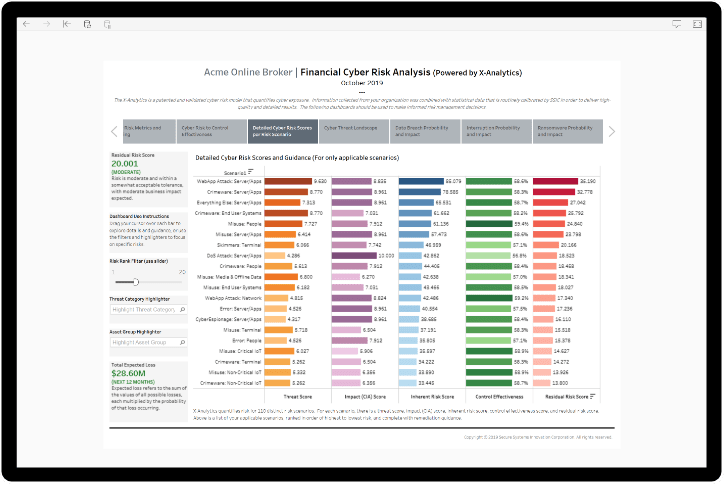
Identify areas of weakness in control effectiveness
Ask “what if” questions about potential control improvements to understand potential benefits
Rank control improvements by their potential for reduction of financial risk exposure
Our risk management approach develops a tailored model of your implicit risk based on your responses to a range of business-related questions and the historic cyber breach data maintained in our partner SSIC’s X-Analytics model for cyber insurance. We then ask up to 650 questions about your cybersecurity controls based on either the Center for Internet Security Top 20 Critical Security Controls or the NIST Cybersecurity Framework. This provides a detailed view of your residual risk and enables the generation of the financial risk exposure results specific to your organization.
Learn More
By submitting this form, you agree to ColorTokens
Terms of Service and
Privacy Policy