Network segmentation has long been a cornerstone of network security. In its early iterations, VLANs (Virtual Local Area Networks) coupled with Access Control Lists (ACLs) formed the foundation of first-generation segmentation. This approach isolated broadcast domains, limiting traffic flow between network segments.
While VLAN ACLs provided a basic level of segmentation, they suffer from several limitations that we will explore in this discussion. While VLAN ACLs offer a valuable initial layer of segmentation, they lack the necessary agility and granularity to fully secure modern networks. This static approach leaves vulnerabilities, such as ransomware potentially infecting the entire network if it spreads between VLANs.
This preface sets the stage for our exploration of segmentation using VLAN ACLs and the subsequent emergence of host-based, software-defined microsegmentation as a superior solution for securing modern networks. We will delve deeper into the shortcomings of VLAN ACLs and how microsegmentation addresses these issues, offering a more granular and dynamic approach to network security.
VLAN Segmentation Using ACL
The traditional approach to segmentation using VLANs and Access Control Lists (ACLs) relies on isolating broadcast domains by assigning devices to specific VLANs based on their function or security needs. ACLs are then configured on routers or switches at the boundaries of these VLANs to control the flow of traffic between them. These ACLs define “allow” or “deny” rules based on parameters like source and destination IP addresses, protocols, and ports. The segments are created based on group of similar assets in a zone.
VLAN segmentation using ACL requires network devices like switches to create VLANs or Zones. This solution groups the physical and virtual interfaces on the device to control traffic that traverses specific interfaces on the network.
Let’s have a look at the implementation process for segmentation with VLANs using ACL:
- Configure all ports as access ports
- Configure switch security
- Control physical access
- Create role-based user accounts
- Restrict telnet ports to account- and password-only access
- Enable port security
- Configure trunks
- Configure VTP/MVRP (recommended to shut it off)
- Create VLANs
- Assign an IP address range to each VLAN
- Assign ports to VLANs
- by IP address (recommended for most static wired networks)
- by MAC address
- by port assignment
- by dynamic assignment (recommended for most wireless networks and shared switch port networks)
- by protocols
- by applications
- Remove all data VLANs from the native VLAN
- Assign unused, connected ports to an unused VLAN
- Configure inter-VLAN routing
- Create and apply L2 ACLs and VACLs
- Create and apply L3 ACLs
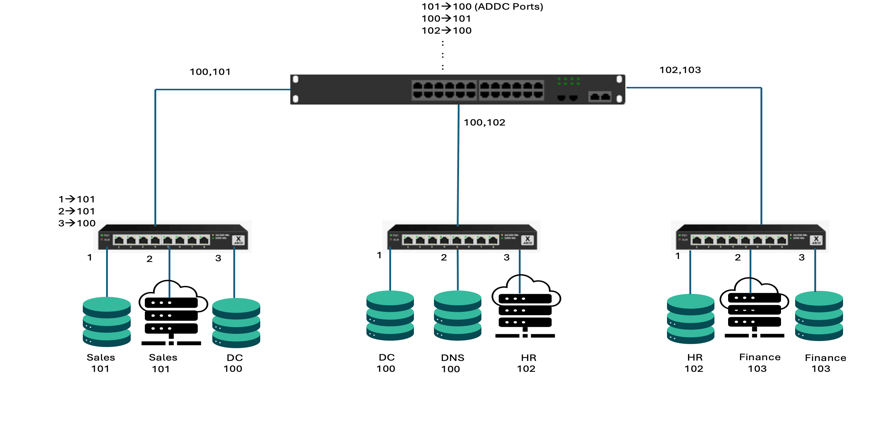
Figure: Segmentation using VLAN ACLs
Issues
- New Server: Port Configuration needs to be updated
- New Switch: ACLs need to be replicated
- No Granular Segmentation with VLANs
- Susceptible to VLAN Hopping, TCAM Exhaustion
VLAN segmentation using ACLs presents scalability issues stemming from the limitations of CAM and TCAM in network switches, causing performance degradation and dropped packets as networks grow. Manual configuration of VLAN membership and access control entries becomes cumbersome and error-prone, hindering agility and responsiveness to security threats. Security issues arise from VLAN attacks like CAM table overflow, enabling attackers to exploit weaknesses and maintain unauthorized access. Complicated setup, administration, and the requirement for additional components increase network complexity and cost. Furthermore, VLANs and ACLs lack granular security policy enforcement and the ability to adapt to dynamic environments, hindering the implementation of Zero Trust principles and dynamic access controls, ultimately compromising network security and resilience.
The Rise of Microsegmentation: Empowering a Future of Enhanced Security and Flexibility
Host-based, software-defined microsegmentation emerges as a game-changer, shifting the focus from securing traditional network perimeters to individually securing each device or endpoint. Also, host-based microsegmentation leverages the native OS firewall to assign distinct sets of rules to each individual host. This approach ensures that security policies are tailored to the specific requirements and vulnerabilities of each system, enhancing overall protection. This enables fine-grained control over network traffic, effectively isolating and securing critical assets from potential threats. Unlike the limitations of VLANs and ACLs with respect to segmentation, microsegmentation empowers each host with its own security rules, offering unparalleled granularity and adaptability.
Imagine a security solution that seamlessly scales with your organization. Microsegmentation achieves this by operating at the host level. As new devices or virtual machines join the network, their security policies seamlessly follow, ensuring consistent and granular control. This eliminates the complexity and limitations of traditional method, which require constant adjustments to accommodate network changes.
Host-based microsegmentation breaks away from the limitations of traditional first generation network segmentation methods that rely solely on network port numbers or IP addresses. Instead, it empowers administrators to define policies based on “tags.” This approach unlocks a new level of granularity, adaptability, robust protection without sacrificing operational efficiency, dramatically simplifies policy management, streamlining the process and eliminating the complexities that plagued traditional network-centric security models. This is particularly valuable in today’s dynamic environments, where IT infrastructure is constantly evolving and expanding
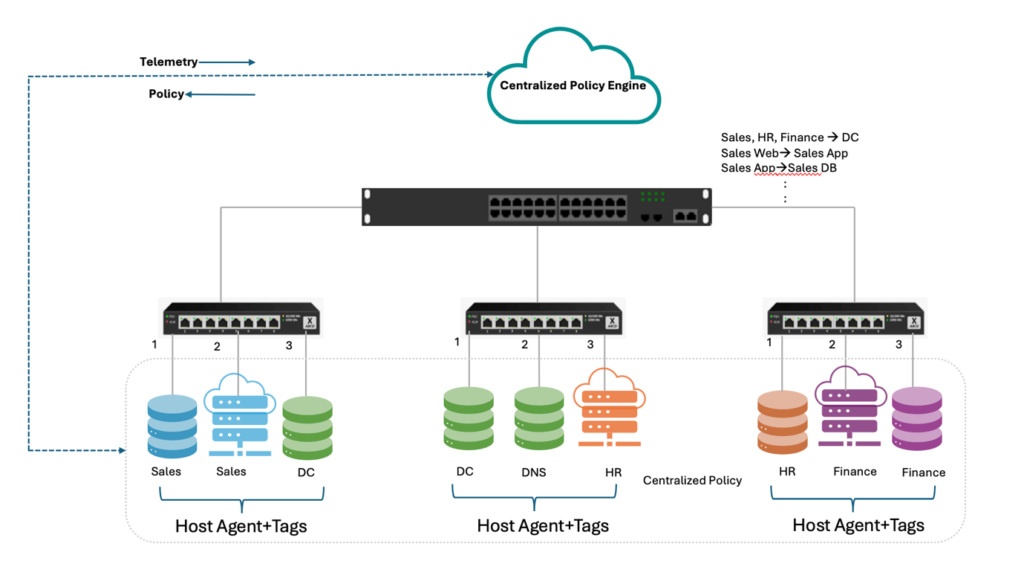
Figure: Host-Based, Software-defined Microsegmentation
Advantages
- Simplified Policies
- Fine Grained Security (Web, App, DB)
- Network Changes have no impact on security policy
Unlock the power of cybersecurity with ColorTokens’ revolutionary host-based microsegmentation solution. Say goodbye to traditional security constraints and embrace a proactive approach that safeguards your digital assets like never before. With ColorTokens Xshield™, you’re not just protecting data; you’re fortifying your entire ecosystem against evolving threats. Ready to elevate your security posture? Contact us now and embark on a journey towards unparalleled protection and peace of mind.