Join us on a 5-minute interactive tour to understand the need for micro-segmentation and how ColorTokens Xshield can help you with this critical Zero Trust strategy.
Guided Tour
Join us on a 5-minute interactive tour to understand the need for micro-segmentation and how ColorTokens Xshield can help you with this critical Zero Trust strategy.
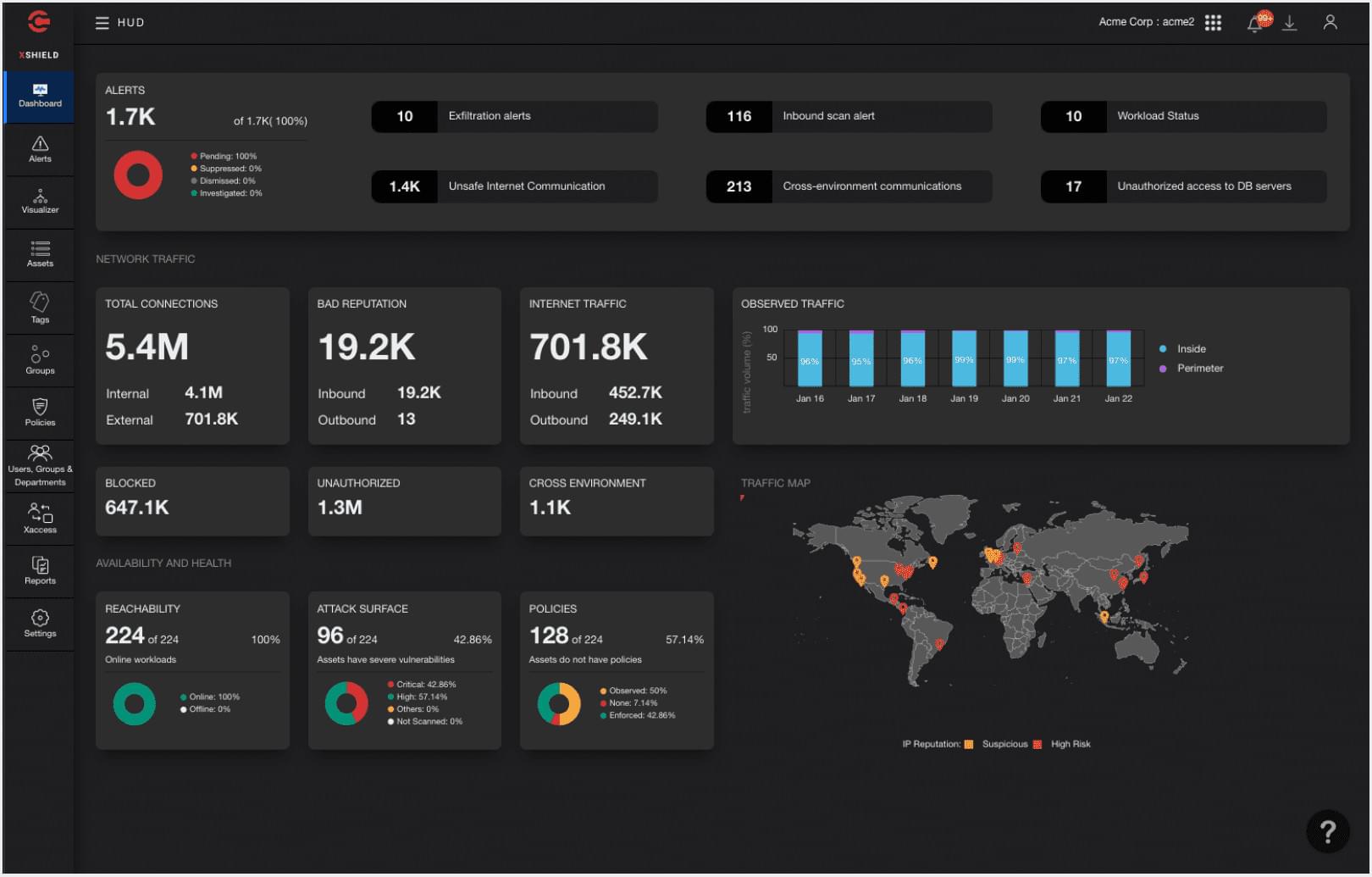
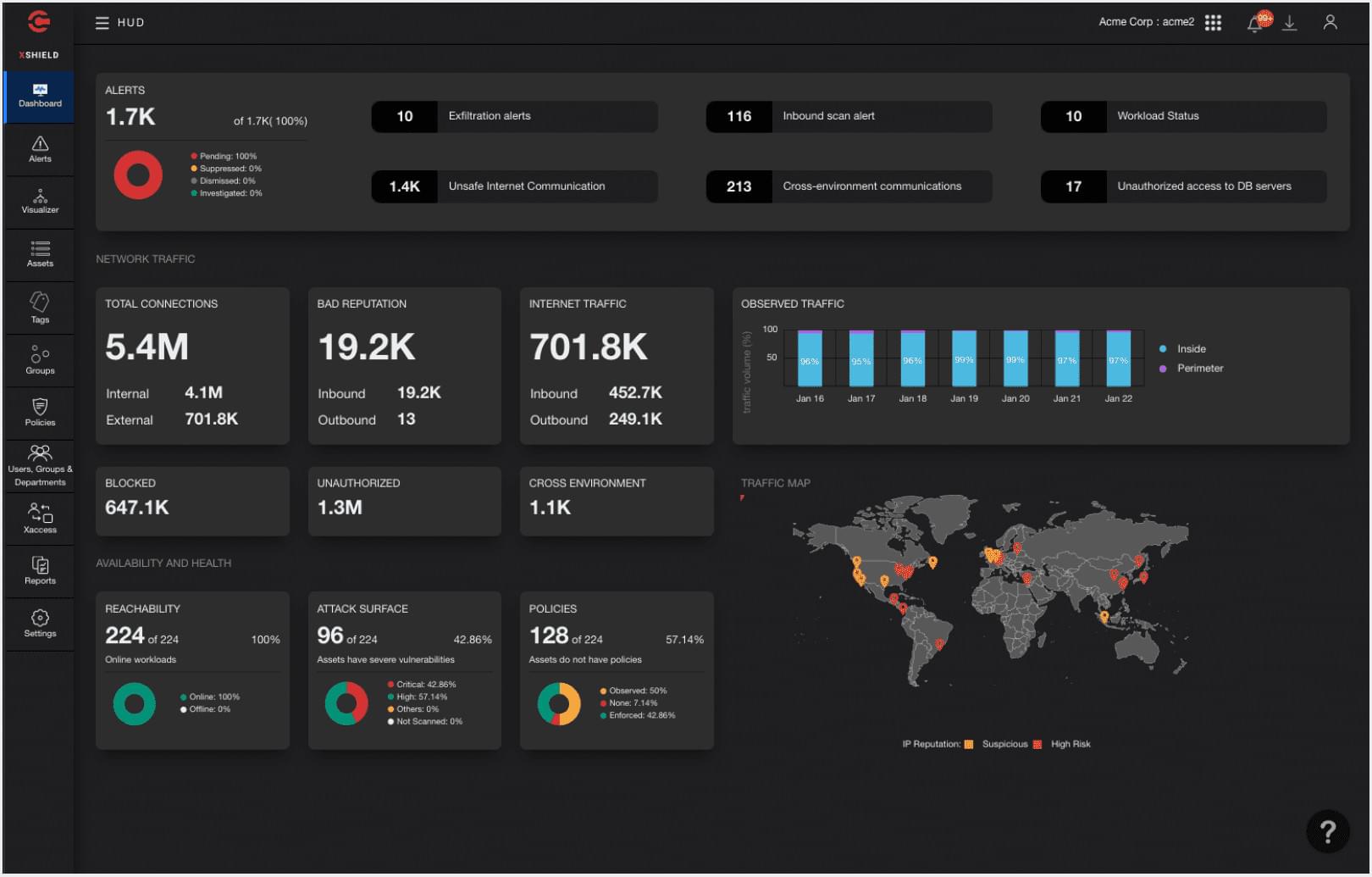
Visualize the traffic mix (east-west vs north-south), attack surface, residual risk, Internet threats, and more.
Visualize traffic in real-time with drill downs to individual sessions. Easily identify abnormal and malicious flows.
Map workloads and endpoints to applications, services and user groups, across clouds and on-premise environments.